Signal interference and signal spoofing are two core concepts in the field of electronic warfare. In simple terms, they can be thought of as the “noise” and the “lies” of the electronic world. Put simply, signal interference makes a device unable to “hear clearly,” while signal spoofing makes it “hear the wrong message.”
To better understand the differences and connections between them, the following sections explain these concepts from several perspectives.
Key Difference: Noise vs. Deception
The fundamental difference between signal interference and spoofing lies in their objectives and methods of operation. The table below highlights their main distinctions.
| Feature | Signal Interference | Signal Spoofing |
|---|---|---|
| Primary Objective | Suppression and disruption: Prevent the opponent’s electronic systems from functioning normally, similar to shining a bright light that makes it hard for someone to open their eyes. | Misleading and control: Cause the opponent’s electronic systems to make incorrect decisions, much like misleading someone with false information. |
| Method of Action | Transmits high-power “noise” signals that overwhelm the real signal and reduce the signal-to-noise ratio at the receiver. | Transmits carefully crafted fake signals that closely resemble legitimate ones, causing the receiver to mistake them for the real signal. |
| Typical Characteristics | Direct but simple: Effective immediately, but easy to detect and often reveals the location of the jammer. | Subtle and deceptive: Much harder to detect and potentially more damaging, but also technically more difficult to implement. |
Common Types and Techniques
After understanding the core distinction, we can look at the typical techniques used in each approach.
Common Signal Interference Methods
Signal interference–often referred to as jamming–acts like an electronic noise generator. Some common approaches include:
- Spot Jamming
A form of “precision attack.” The jammer targets a specific communication frequency with a narrow bandwidth signal, making it efficient while minimizing interference to friendly systems. - Barrage Jamming
A “blanket attack.” The jammer broadcasts powerful interference across a wide frequency band in an attempt to block all communications within that range. While effective, it consumes more energy and may also disrupt friendly signals. - Sweep Jamming
The interference frequency continuously scans across a spectrum, similar to a searchlight sweeping an area. This allows multiple channels to be disrupted in sequence. - Follower Jamming
Designed to counter frequency-hopping communications. The jammer detects and follows the hopping pattern in real time, applying interference at the exact frequencies being used.
Common Signal Spoofing Techniques
Signal spoofing operates more like a skilled deceiver, creating misleading signals in different ways. Typical methods include:
- Replay Spoofing (Meaconing)
Method: Authentic satellite navigation signals are received, slightly delayed, and then retransmitted from another location with stronger power.
Purpose: Nearby receivers lock onto the stronger delayed signal and calculate an incorrect position or time.
Characteristic: Since the signal itself is genuine–only delayed–it is extremely difficult to detect. - Signal Generation Spoofing (Spoofing)
Method: Instead of replaying real signals, the attacker generates entirely fake navigation signals that follow the expected format.
Purpose: By controlling the fake signals, the attacker can cause the target receiver to calculate almost any desired location.
Characteristic: Technically challenging, and nearly impossible against encrypted military signals. - Gradual Synchronized Spoofing
Method: An advanced form of generation spoofing. The attacker first transmits signals synchronized with the authentic ones at a similar power level, causing the receiver to unknowingly track them. The parameters are then slowly and gradually adjusted.
Purpose: The receiver’s calculated position is smoothly guided to a predetermined location without triggering suspicion.
Characteristic: Highly covert and potentially very dangerous, making it a key focus of future navigation warfare research.
Real-World Applications and Impact
These technologies play important roles in the real world, particularly in military and security contexts.
- Military Applications
Disrupting enemy communications, forcing drones to land through spoofing, or altering missile trajectories are all examples of modern electronic and navigation warfare. - Civilian Security Risks
Interference or spoofing of navigation and timing systems used in aviation, maritime operations, and critical infrastructure–such as power grids or financial networks–can lead to serious consequences, including aircraft navigation errors, ship collisions, or communication failures. - Everyday Misuse
Illegal signal jammers used in unauthorized wireless devices or cheating equipment can disrupt public mobile networks and even pose risks to aviation safety.
Defensive Measures
As these threats evolve, various countermeasures have been developed:
- Multi-source Data Fusion
Satellite navigation data can be cross-checked with inertial navigation systems (INS). Large discrepancies between them may indicate spoofing. - Signal Authentication
Some navigation systems include encrypted authentication features–such as the OS-NMA mechanism in the Galileo system–allowing receivers to verify signal authenticity. - Anomaly Detection
Monitoring characteristics such as signal direction, strength, and consistency can reveal suspicious patterns. For example, if signals from all satellites appear to arrive from the same direction, something is clearly wrong.
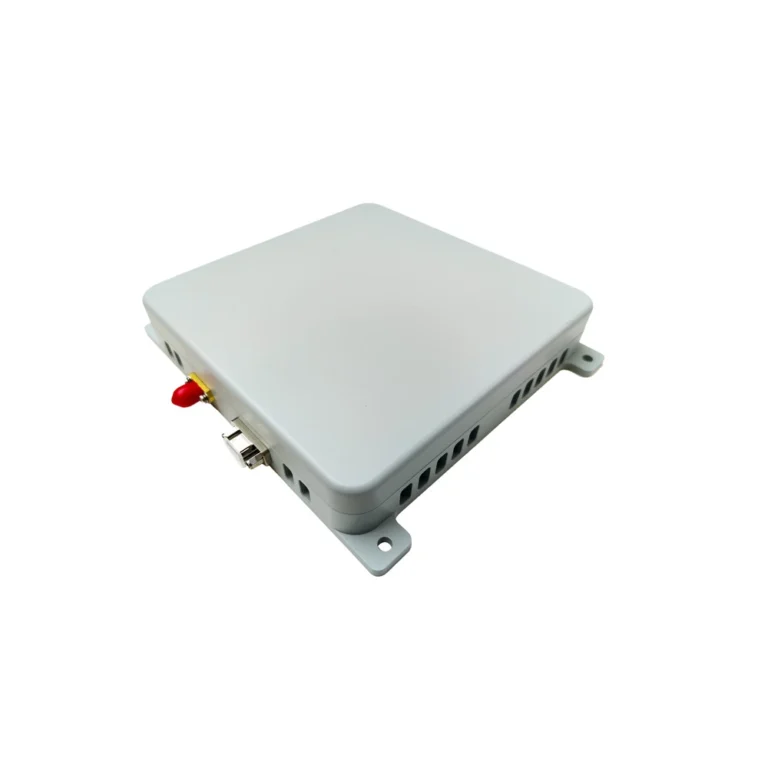
A CRPA (Controlled Reception Pattern Antenna) uses multiple antenna elements arranged in an array to determine precisely the direction from which an interference signal is arriving. Once the interference direction is identified, the CRPA processor dynamically adjusts the antenna’s reception pattern in real time, creating an area of extremely low gain in that specific direction–much like carving out a blind spot on a radar display. This technique is known as “nulling” or “null steering.”
No matter how strong the interfering signal may be, as long as it originates from that direction, its impact on the receiver can be suppressed to a minimal level.
By upgrading a single “ear” into a coordinated antenna array, CRPA technology gives navigation systems a form of spatial awareness. The system can not only “hear” incoming signals but also determine where they are coming from. This capability allows it to actively filter out disruptive “noise” and deceptive “false signals” in the complex electromagnetic environment of modern electronic warfare, protecting the integrity of positioning and navigation data–the system’s final line of defense.
Today, CRPA technology is gradually moving from military applications into the civilian sector, particularly in fields such as autonomous driving and civil aviation, where reliable navigation signals are critically important.